I wish I could say it was some genius master cracker that tricked Amazon, Apple and Twitter to get into my account, but unfortunately it was just plain carelessness.
Here’s one way to do it…
You probably remember the recent Twitter fiasco where Naoki Hiroshima lost his $50,000 Twitter username due to some social engineering and blackmail threats.
Prior to the actual hack, Naoki had been offered up to $50,000 to turn over his username (it was a 1-letter username, which for some reason made it extremely valuable to some). He declined the offers, but fell victim when an attacker gamed Paypal and GoDaddy to piece together enough information about him to gain acces to his email and domains. At that point, he gave in and gave over the login info to the scammer (you can read the follow-up with tips on how to prevent his here: Picking up the pieces after the @N Twitter account theft).
This was sophisticated and somewhat low-tech at the same time, as the scammer actually picked up the phone and called to run his game.
In my case it wasn’t anything so grandiose. My account was hacked because I left the door open for them.
Check Those Twitter Apps!
Now, I wouldn’t exactly say my account is worthless…but it certainly hasn’t fielded any offers for $50,000 (although for some reason my YouTube username has had two requests…odd). Anyway -bottom line is this: whenever you allow some app access to your Twitter account, someone else can come along and hack them – at this point access to your account has already been granted.
The proof of this is found in the Buffer security breach from last year. Many of us used the service to schedule our tweets, trusting them enough to allow them to post on our behalf.
Once they were hacked, the “evildoers” began spewing a stream of weight-loss spam junk tweets out into people’s feeds, and some to Facebook as well.
I was actually affected by this, but only one tweet went out. Whew! I figured I lucked out.
Did NOT Learn my lesson
Any reasonable person would have stopped, taken stock right then and really thought about what kind of services they would allow access to their twitter account.
Not me.
A couple of weeks back, I got a notice from Twitter that my account may have been compromised:

Wait, what??
I quickly checked my feed. Yes, indeed there was something stupid there:

I deleted the tweet after this. But me being me, I felt it was only right to set the record straight to my beloved followers:
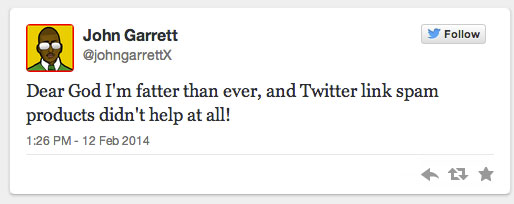
So that fixed the immediate problem, and hopefully any of my followers who saw the fake tweet realized the futility of trying to lose weight without working for it.
Now, back to Twitter. They reset my password and told me to change it again to something I preferred.
Hmmmm. My password had already been a 14-digit strong password generated through lastpass.com, so I doubted my password had been compromised. Not that this is by any means foolproof, it’s just that I didn’t think my Twitter account would warrant the kind of effort it would take to crack the password.
After I reset my password (this time using an 18-digit strong password), I decided to check and see if Buffer had been hacked again. Well, nope.
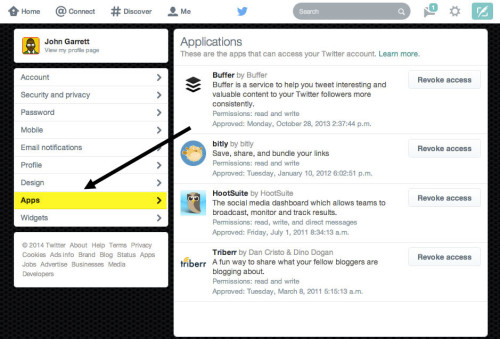
Then I thought, let me just check in the app section of my Twitter account and see what other services might haven been compromised. I logged into my account, then clicked the “Apps” link on the left.
When I got in there, I was shocked: I had FIFTY-SEVEN (57!) apps listed. Many of which had access to post as me.
Holy Crap. I’ve been consistently using my account since 2010, and many of those apps dated back that far. When I looked up some of the apps, the companies that made them didn’t even exist anymore. For the ones that were still there, any one of them could have been compromised, or it could even be a case like the recent Google Chrome extensions adware debacle, where apps were being bought out by companies who then used the installed userbase as an audience for their malware. No way to tell from my end.
If you’re doing the blogging thing, you probably know how it goes – you try one system, see if it works for you, then pick another one, so on and so on. Pretty soon you forgot that you meant to go back and delete those unused services. That’s what I did over a span of four years.
I have absolutely no idea which one of them was doing the spamming, but it didn’t matter, I went scorched earth in there and blasted everything. By the time I was done, I had only four things left. That’s all I was actually using:
Of the four left, Bit.ly might get dropped, because I rarely use it, so that’ll be three – and I can’t imagine it would grow much more than that. Things will be staying lean and mean from now on.
The Wrap Up
So that’s it, guys. If you’ve been adding apps all willy-nilly over the years like me and you haven’t done your due-diligence in cleaning them out, get in there now and see what horrors are lurking in the depths of your Twitter account.
If you don’t have a particularly engaged following, you could be tweeting out spam for days (or longer) before you catch onto it.
Hopefully this helps someone and keeps those Twitter streams spam-free. See you guys next time…

Hey John! A couple of years ago, I added a reminder to my Google Calendar, which was a simple link to http://mypermissions.org/
Once a month, I would go through FB, Twitter and Gmail permission pages and cancel stuff.
That’s a shame that you hit the Ketchup number on Twitter – that opened up a wormhole into Alpha Centauri, allowing Shiznood Zlick to come in and do her dirty dancing on your digital footprint. As a Freelance artist/web designer/developer Extraordinaire, you shoulda known better. But, see la vee, no?
Cheers,
Mitch
Lol Mitch, yes that’s pretty much what happened!
Thanks for a great suggestion on that site. It looks like mypermisions.org must have migrated to http://mypermissions.com now. I went through and found quite a few more apps that I had to delete. Gotta be more careful…!
Hey John,
I know nothin’ ’bout no migratin. I get migraines, though. Is that the same thing?
When I click on .org I get right to the list of links. The .com seems to be targeted at App makers.
Yesterday, I tried to duplicate your scorched earth, but I just couldn’t bring myself to delete IFTTT, Powerbot and Rapportive!
Cheers,
Mitch
Migrations are definitely the cause of migraines, that much I know!
For some reason when I click on the .org it times out for me, but going to the .com and clicking the “Start Scanning” seemed to do show all the apps I had lurking out there.
I had to add it to Chrome first before it worked, but it’s all good now. I’ve got to really get on that IFTTT!
Weird. Well, anyway, IFTTT is fun. I don’t really use at the moment, but I see the potential.
Cheers,
Mitch
I added a reminder to my Google Calendar, which was a simple link
The best way change the password every 3 months and use both letters and digits.